THE #1 MOBILE HACKING COURSE TO BECOME A CERTIFIED MOBILE SECURITY EXPERT
WE TEACH YOU OFFENSIVE
MOBILE SECURITY SKILLS!
Our Way of Teaching
What we do
Unique Learning Paths
Learn from experts
Video Conferencing
Built by Professionals
The Mobile Hacking Lab Approach
Start With Our Free Courses!
Get Access To All of Our Material
Whether you're just starting out in the field of mobile security or looking to expand your skillset, our subscriptions have something for everyone.
Real Arm Devices
Why We Are the Best
Benefits Of Our Courses
Exclusive and Specialized Content
Real-World Application and Hands-On Training
Expert-Led Training and Support
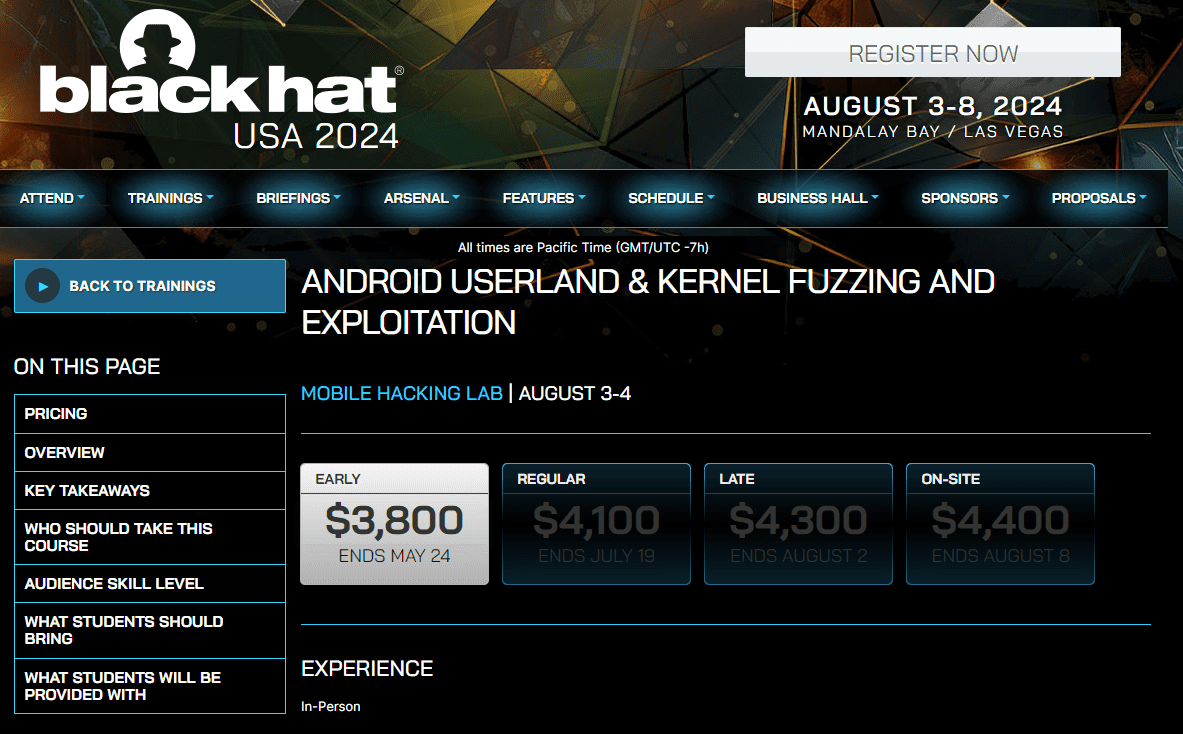
Presented at Multiple Black Hat Conferences
Recognized & Trusted by Industry Leaders
Try Our Course Out for FREE!
What Our Students Think About Us
Mobile Hacking Course Experiences
Shared by Our Students
Highly recommended!"
Director of Security Research
at Dark Wolf Solutions
Application Security Engineer
at Nord Security
Highly recommend!"
Niv Roda
Application Security Engineer
at Apps Flyer
Build Your Skillset
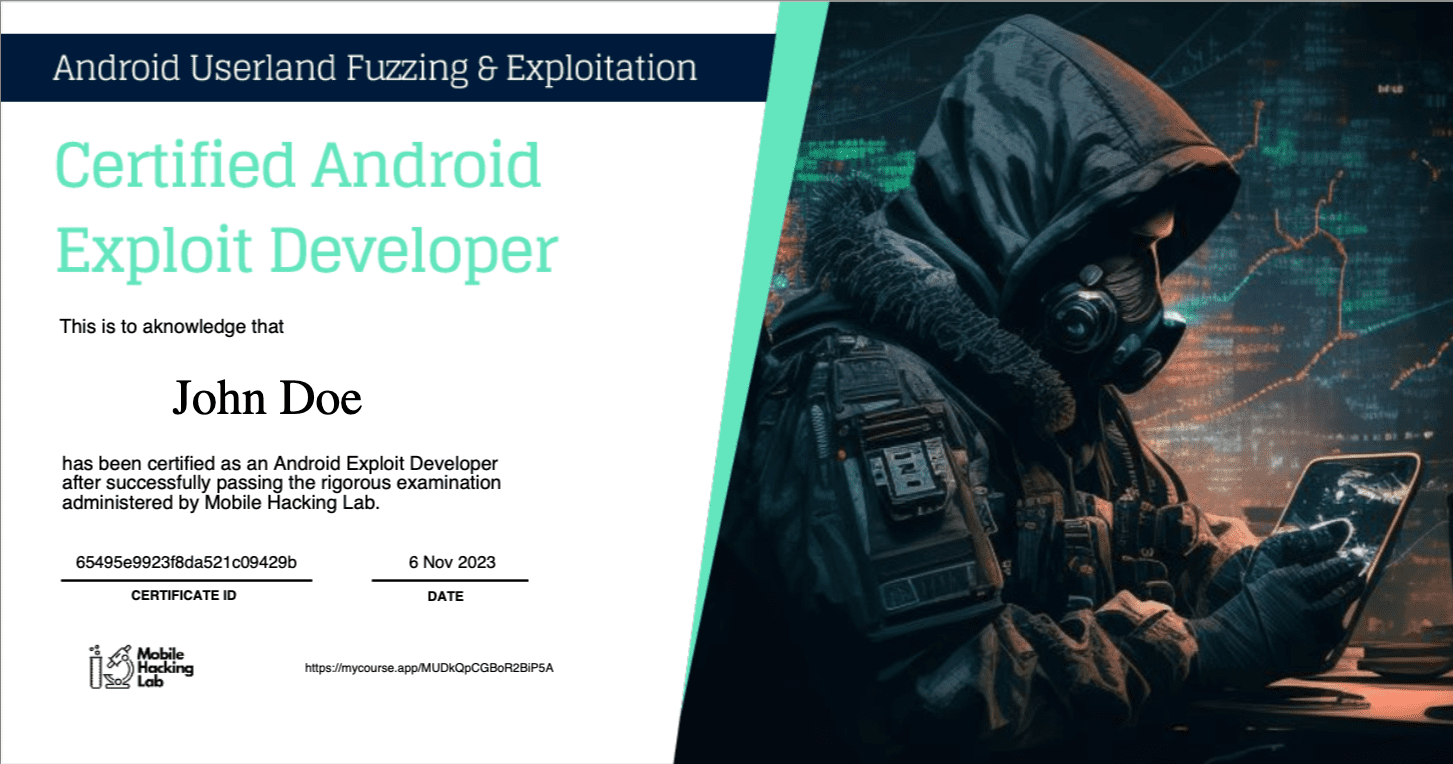
Certification Included
-
Get The Job You Want
With our certification you can promote your skillset to business recruiters so that you can get the job you want.- Build your skillset and your CV
-
Become a Certified Mobile Security Expert
- Get the job you've always wanted
-
Get to Know Us
The Team
Our Most Prized Possessions
Start Learning With Us!
Dive into the world of Android security with our tailored course packages designed to suit your learning needs and goals:
Each practical lab experience is an opportunity to implement what you've learned and solidify your expertise. Upon completion, earn your Certificate of Completion to showcase your practical skills and theoretical knowledge.
Ready to secure your spot in the forefront of mobile security? Enroll in the package that best fits your journey today.
Our Free Knowledge
Mobile Hacking Lab Blog
FAQ's
Do I need physical devices for the course?
What are the skills required to follow along?
Mobile Hacking Lab's courses are designed for accessibility, requiring no expert knowledge to begin. While familiarity with C/C++ code is expected, and basic Python skills are beneficial, our curriculum is structured to enhance your understanding of Python scripting for exploit development, ensuring learners of all levels can progress effectively.
What version of android/iOS will be targeted in the course?
Should I know Arm assembly?
Prior knowledge about Arm64 Assembly is not required as the Android Userland Fuzzing and Exploitation course has an Arm64 Programming mini course that teaches basics and also Arm64 shell coding.
